Text
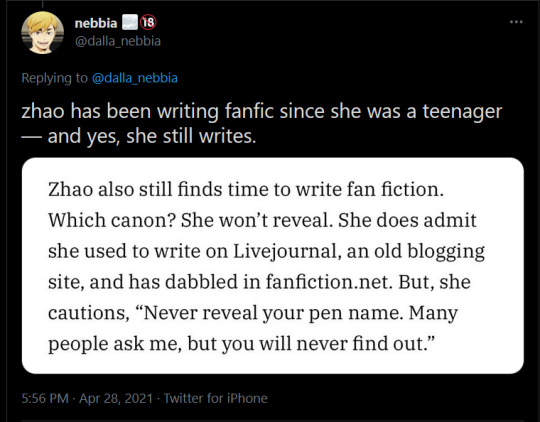

Chloé Zhao, who just won an Oscar for best director, writes fanfiction.
That's the kind of validation I needed in my life. Thank you, ma'am.
144K notes
·
View notes
Text
writer’s block (dry) = no desire to write, no ability to write (bearable)
writer’s block (wet) = HUGE desire to write, no ability to write (very evil)
70K notes
·
View notes
Text
Well since you all asked nicely...
Time you all learn how to get into being a hacker~!
Advance warning this will be a long post and as of typing this idk if tumblr has char limits so might need to continue in reblogs?
Right, so. You may be asking "How do I get into hacking?" and find yourself here because of it.
The answer is you just did it. Right there. By clicking that keep reading link you have just entered the world of hacking, because curiosity is everything. The innate urge to learn more, to know more, that is what hacking comes down to. You do more than just using a system, you question it. Ask yourself, what does the system do when i input these characters? How does it take my input and translate it into the function? Where does it store information in what way?
Have you ever tried inputting unexpected text into a field? For example, say a website asks for a particular input like your name, but instead you start putting in numbers or unexpected unicode. That right there is, by definition, the poking around that hacking uses. You're experimenting with unexpected use-cases. Often times if you try this, you may end up finding interesting results. In my example here, say instead of your name, you put ../../../../etc/passwd into the field. Suddenly when you hit enter, you get hit with a result of a bunch of names and data. That is a hack. The database to control the storage of your name instead received a command to back out of that database, and go into the etc folder to retrieve the passwd folder, which houses user data from that system. This, of course, assumes the system is running Linux, but it is an example. All hacking is, is poking around in ways the original programmer couldn't expect to find interesting results and broaden your access into things you shouldn't have.
Now, this is all well and good, but what if you want an actual way to learn this in person? Well the good news is there are plenty of legal avenues to get into hacking and broaden your experience! Personally I use HackTheBox for my CTFs through their labs. That means they run a thing called Capture The Flag, where they give you a single IP and you have to explore that system to find two different flag files to win. They also have competitive CTFs I have yet to try, but I do have a competitive tournament coming up next month for it. Then they also have the academy to teach you more via both hands-on methods and reading work. If you know next to nothing and want to get started in a safe learning environment, you can try out their academy or my next resource.
TryHackMe! This website is more learning focused, and I have been taught a lot of what I know through it! It has free lessons along with premium ones for a subscription, so just know that only a selection of what you can learn here is free, but I do recommend them if you do feel like paying for that extra bit, as I would say what I learned from it was worth it and they focus on both offensive hacking, which I do, as well as the blue side for defensive hacking and even things like digital forensics if you're interested in that!
HackThisSite. No really, hack it! This website is a legal playground to try out scenarios from the unlikely to the realistic in varying difficulties to put your skills to the test!
There's many, many more resources to look into as well, those are just the first few off the top of my head. Beyond this, I'd say constantly stay up to date in cybersecurity news and read up on new large scale attacks, as the entire industry is a constant arms race with exciting twists to learn about! Beyond that there is no one right way to go about hacking, and there's never a stupid idea to it either!
Now, all this is well and good, but what about a real case example? Well luckily for you all I happen to have a machine up and running to show off a case example of a CTF in action. Today i'll be showing you the "Lame" box from HackTheBox, the first machine they ever published, now retired. I can access it thanks to VIP.
First thing's first, I'm using a laptop that I stripped of Windows 11 in favor of Linux, and specifically Kali Linux being the exact distro. If you're wanting to get into hacking at the VERY least use a VM with linux, but i beg of you dont use windows. You're asking for trouble both in terms of lack of tools and in terms of vulnerability. You're putting a VERY large target on your back by using Windows because of how vulnerable it is. Kali Linux is a nice option as it comes pre-built with tools, but if you want something more user friendly you can go for Parrot OS.
Once the OpenVPN connection is active and we have the Lame machine up and running, it gives us an IP and nothing more. The first thing you will want to do when this is the case is to use a tool called Nmap to scan that IP for active TCP ports. This shows you what open, and sometimes closed, connections that machine is running, along with information about them. I usually use the command with these particular flags. nmap -sV -Pn -p- (ip)

It will output the ports we want to see, dont worry about how much text there is, we're focusing on just a small segment saying port numbers and a description of them
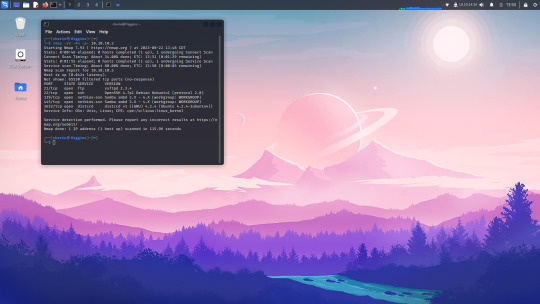
Now that's interesting, looks like this is running Samba SMBD on ports 139 and 445, and thanks to a google search I know this is a vulnerable version. We'll take the quick route and just use a tool called Metasploit. In a typical run metasploit wont have what you need, but for the sake of time and post length, i'll just boot that up by running "msfconsole" and running a search for our exploit. On finding the one I need I select the payload.
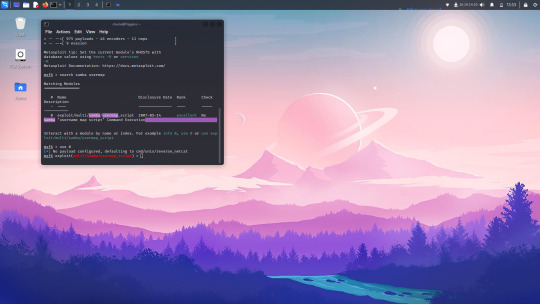
Next up, we need to equip the options for it, setting who our target is and where to send the information back to, in this case my VPN's IP.
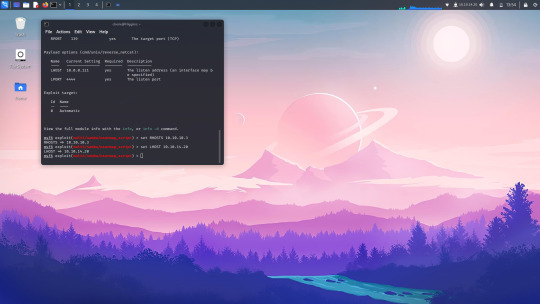
Once that's done, you simply say "run" and it will go! And what do you know, i'm in the system as a root user, aka full administrative privileges with access to both the user and root flag! In a typical CTF there are many more steps including usually getting into the user first, then exploiting into root. I, however, took the shorter route this time.

(The flags change every run so you cant just copy paste them from my run.)
And that's that, machine conquered! We did it! Of course, in the real world of hacking there are many more steps, and it can even take multiple days to get everything you need from a target in a stealthy manner. The faster you move, the louder you are.
Now you know the basics though! Get out there and learn, google will be your friend and its never wrong to ask questions. My DMs are open if you have more to ask or just wanna talk hacking! :3
Legal, illegal, who cares im not a cop, have fun and stay curious~!
3K notes
·
View notes
Text
That “blank look” in my blind eyes? (Please stop saying this)
Hey quick question sighted people- What is this “blank look” that blind people have? I’ve never seen it in person myself and every time I read a character realizing another character is blind based on “the blank look in their eyes” I just sigh.
Eyes are rarely blank. If ever. Even someone with zero eyesight doesn’t have blank eyes. Like look at Molly Burke, she only sees light and shadow but her eyes are just as full of emotion as a sighted person’s. Granted, she had 14 years of some vision (though never sighted) and took acting classes, which helps her seem more sighted than she is, so…
What about someone who is born blind and has no idea of what “normal facial expression is”? Well, also not true. Blind babies still know how to smile and show all six of the basic universal facial expressions. It’s innate, instinctual. And maybe their eyes don’t focus on something specific, but I couldn’t describe it as blank. It’s not blank.
What about blind people who have obvious, visible problems with their eyes. Like eyes that are cloudy or misshapen or point in separate directions. I mean, those people are more obviously blind, but saying their gaze is blank is kind of weird, kind of insulting.
And I’m sorry, but sighted people aren’t really observant enough to just “realize a stranger is blind by the way they act and move” like, that doesn’t happen. I have people look at my cane and sunglasses and not realize that means I’m blind, or people who have been told I’m blind but regularly forget because I don’t seem blind.
Blindness is a visible disability, but it’s also equally invisible. Take away my cane and my sunglasses, put me in a room full of strangers with average lighting, and let’s count down how long it takes people to realize I’m blind, even with hinting and obvious self deprecating blind jokes.
Anyway, I’m sorry. I know “she realized the boy was blind by the blank look in his eye” doesn’t fly because eyes can’t be blank. Sorry, you either got to have someone mention the character is blind (preferably having the blind character introduce themselves and talk like a normal person) or you’re just gonna have to deal with the fact your character can’t tell a sighted person and a blind person apart.
I mean, does your character have the cane? Or a guide dog? I hope that’s sufficient to tell your character that person’s blind, but if they really need to lean into the blind person’s personal space and thoroughly examine that so called blank look in their eye, by all means, go ahead *sarcasm*
1K notes
·
View notes
Text
i feel like if you stabbed an angel the blood trail would look like this


59K notes
·
View notes
Text
people who think writers are in control of the story clearly have never spoken to a writer
6K notes
·
View notes
Text
writing fanfiction is wild. i could make these two characters do anything. i could make them get married rn. the possibilities are endless
33K notes
·
View notes