Text
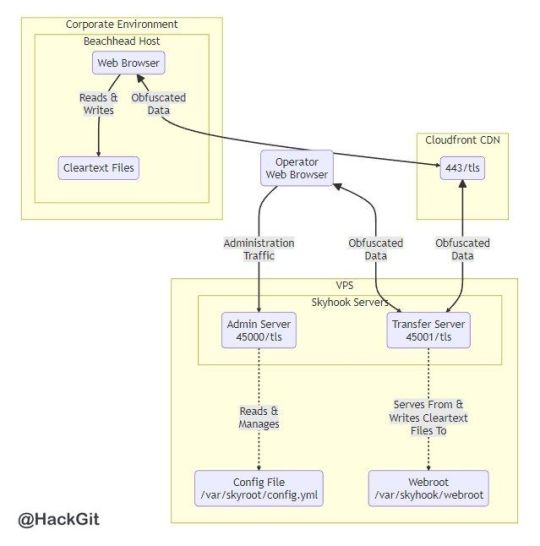
[Media] Skyhook
Skyhook
A REST-driven web application used to smuggle files into and out of networks defended by perimeter controls that inspect and act on traffic perceived to contain malicious content.
https://github.com/blackhillsinfosec/skyhook
#infosec #pentesting #redteam
8 notes
·
View notes
Text
[Media] EnumStrike
EnumStrike
Cobalt Strike Aggressor script to automate host and domain enumeration.
https://github.com/DallasFR/EnumStrike
#infosec #pentesting #redteam

3 notes
·
View notes
Text
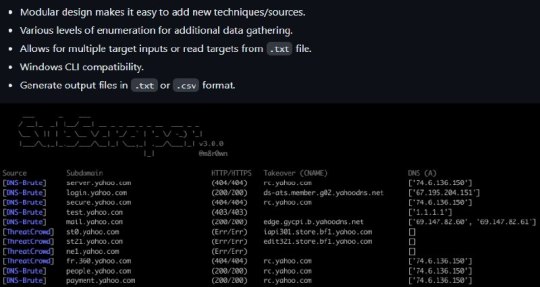
[Media] SubScraper
SubScraper
Perform subdomain enumeration through various techniques and retrieve detailed output to aid in further testing.
https://github.com/m8sec/subscraper
#infosec #pentesting #bugbounty
0 notes
Text
[Media] CVE-2023-31726
CVE-2023-31726
POC for CVE-2023-31726: AList 3.15.1 is vulnerable to Incorrect Access Control, which can be exploited by attackers to obtain sensitive information.
https://github.com/J6451/CVE-2023-31726
#cve #poc #infosec

0 notes
Text
[Media] CVE-2023-31779
CVE-2023-31779
Stored XSS vulnerability exists in the "Reaction to comment" feature. An attacker with user privilege on kanban board can execute JavaScript code in the browsers of users who open card with malicious reaction.
https://github.com/jet-pentest/CVE-2023-31779
#cve #cybersecurity #infosec

0 notes
Text
[Media] opera-proxy
opera-proxy
Standalone Opera VPN client. Just run it and it'll start a plain HTTP proxy server forwarding traffic through "Opera VPN" proxies of your choice. By default the application listens on 127.0.0.1:18080.
https://github.com/Snawoot/opera-proxy
#VPN #infosec #privacy

1 note
·
View note
Text
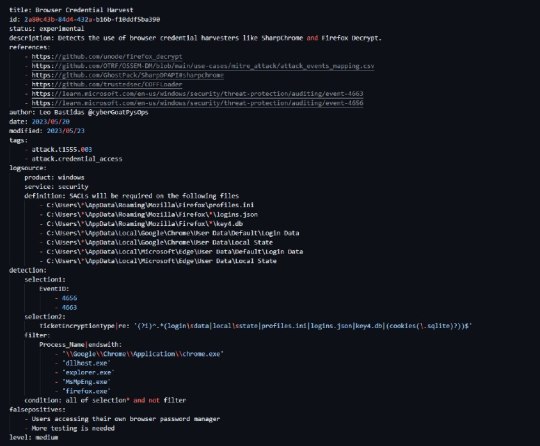
[Media] Detections - Browser Credential Harvesting
Detections - Browser Credential Harvesting
Web browsers today allow users to store their username and passwords, directly to log into their application of choice. Threat actors can retrieve these credentials using either the Windows API or decrypting specific files. This detection strategy focuses on specific files that are needed by the attacker to retrieve the user’s web browser stored credentials.
https://github.com/cybergoatpsyops/detections/tree/main/techniques/webCredentialHarvest
#cybersecurity #infosec
4 notes
·
View notes
Text
[Media] Keyhacks
Keyhacks
A repository which shows quick ways in which API keys leaked by a bug bounty program can be checked to see if they're valid.
https://github.com/streaak/keyhacks
#infosec #pentesting #bugbounty

1 note
·
View note
Text
[Media] ProcOpen-PHP-Webshell
ProcOpen-PHP-Webshell
Experience the power of a PHP webshell designed to overcome the limitations of blacklisted system/exec functions.
https://github.com/d4rkiZ/ProcOpen-PHP-Webshell
#infosec #pentesting #redteam

0 notes
Text
[Media] PCAPeek
PCAPeek
A proof-of-concept re-assembler for reverse VNC traffic such as IcedID & Qakbot's VNC Backdoors.
https://github.com/0xThiebaut/PCAPeek
#cybersecurity #infosec

1 note
·
View note
Text
[Media] Shellcrypt
Shellcrypt
A single-file cross-platform quality of life tool to obfuscate a given shellcode file and output in a useful format for pasting directly into your source code.
https://github.com/iilegacyyii/Shellcrypt
#infosec #pentesting #redteam

2 notes
·
View notes
Text
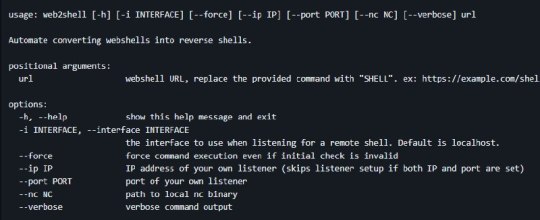
[Media] web2shell
web2shell
A Python program used to automate converting webshells into reverse shells. If you regularly do CTF, HTB, or red teaming you've probably spent a good chunk of time testing payloads to convert a webshell into a reverse shell. This tool aims to simplify this process.
https://github.com/ejedev/web2shell
#infosec #pentesting #redteam
4 notes
·
View notes
Text
[Media] Shaco
Shaco
Shaco is a minimal C linux agent for Havoc. Shaco communicate with http to the server using hardcoded socket
https://github.com/souzomain/Shaco
#infosec #pentesting #redteam

0 notes
Text
[Media] CVE 2023 25690
CVE 2023 25690
Proof of concept - mod_proxy vulnerable configuration on Apache HTTP Server versions 2.4.0 - 2.4.55 leads to HTTP Request Smuggling vulnerability.
https://github.com/dhmosfunk/CVE-2023-25690-POC
#cve #poc #infosec
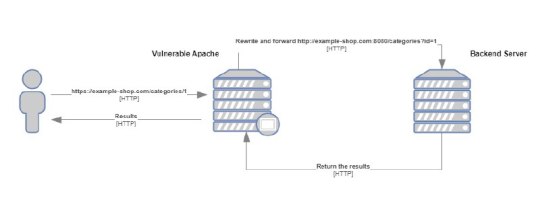
0 notes
Text
[Media] Damn Vulnerable Bank
Damn Vulnerable Bank
Damn Vulnerable Bank is designed to be an intentionally vulnerable android application. This provides an interface to assess your android application security hacking skills.
https://github.com/rewanthtammana/Damn-Vulnerable-Bank
#cybersecurity #infosec #pentesting

0 notes
Text
[Media] CVE-2023-2822
CVE-2023-2822
Simple flask application to implement an intentionally vulnerable web app to demo CVE-2023-2822.
https://github.com/cberman/CVE-2023-2822-demo
#cve #cybersecurity #infosec

2 notes
·
View notes
Text
[Media] NixImports
NixImports
A .NET malware loader, using API-Hashing and dynamic invoking to evade static analysis.
https://github.com/dr4k0nia/NixImports
#malware #cybersecurity #infosec
0 notes