#firewall network security
Text

Best Cyber Security Services- NewGig Secure Solutions
#firewall#security#network security services#network security solutions#network security market#antivirus
2 notes
·
View notes
Video
youtube
#1 Free Network Security Tutorial | CheckPoint CCSA | EVE-NG In Google Cloud
#Free Network Security Tutorial#CheckPoint CCSA#CheckPoint#CheckPoint Firewall#P1#CheckPoint Firewall P1
2 notes
·
View notes
Text
In 2024, World Milk Day will be celebrated with a theme focusing on celebrating the vital role dairy plays in delivering quality nutrition to nourish the world.
#eeka#consultancy#services#bangalore#networking#security#firewall#happy#jobs#ecs#mik#milkday#milkman
0 notes
Text
Fortinet 𝐅𝐨𝐫𝐭𝐢𝐆𝐚𝐭𝐞 𝟏𝟎𝟎𝐅, 𝐅𝐨𝐫𝐭𝐢𝐆𝐚𝐭𝐞 𝟖𝟎𝐅, 𝐚𝐧𝐝 𝐅𝐨𝐫𝐭𝐢𝐆𝐚𝐭𝐞 𝟔𝟎𝐅 Firewalls

🔒 Strengthen your #networksecurity with our latest lineup of #FortinetFirewalls! 💪 Whether you're safeguarding a small business or a large enterprise, we've got you covered with the 𝐅𝐨𝐫𝐭𝐢𝐆𝐚𝐭𝐞 𝟏𝟎𝟎𝐅, 𝐅𝐨𝐫𝐭𝐢𝐆𝐚𝐭𝐞 𝟖𝟎𝐅, 𝐚𝐧𝐝 𝐅𝐨𝐫𝐭𝐢𝐆𝐚𝐭𝐞 𝟔𝟎𝐅.
Here's why they're your best defense:
🛡️ 𝐀𝐝𝐯𝐚𝐧𝐜𝐞𝐝 #𝐓𝐡𝐫𝐞𝐚𝐭𝐏𝐫𝐨𝐭𝐞𝐜𝐭𝐢𝐨𝐧: Combat cyber threats effectively with integrated #security features like #antivirus, intrusion prevention, and web filtering.
🔐 𝐒𝐞𝐜𝐮𝐫𝐞 𝐂𝐨𝐧𝐧𝐞𝐜𝐭𝐢𝐯𝐢𝐭𝐲: Keep your network safe with robust #VPN capabilities, ensuring secure connections for remote workers and branch offices.
🚀 𝐇𝐢𝐠𝐡 𝐏𝐞𝐫𝐟𝐨𝐫𝐦𝐚𝐧𝐜𝐞: Experience blazing-fast performance and seamless scalability to meet the demands of your growing #networkinfrastructure.
📈 𝐒𝐢𝐦𝐩𝐥𝐢𝐟𝐢𝐞𝐝 𝐌𝐚𝐧𝐚𝐠𝐞𝐦𝐞𝐧𝐭: Manage your security policies effortlessly with our intuitive interface, making network administration a breeze.
Upgrade your defenses today and stay ahead of evolving #cyberthreats with Fortinet #FortiGatefirewalls!
𝐑𝐞𝐚𝐜𝐡 𝐮𝐬 𝐨𝐮𝐭 𝐚𝐭: +𝟗𝟕𝟏 𝟓𝟔 𝟓𝟓𝟏 𝟑𝟑𝟏𝟓
𝐂𝐡𝐞𝐜𝐤 𝐡𝐞𝐫𝐞 𝐭𝐨 𝐛𝐮𝐲: https://costtocost.ae/shop-for-the-best-quality-firewall-in-dubai/
#uae#dubai#business#it support#firewalls#Fortinet firewalls#fortinet fortigate firewalls#network security#cybersecurity#costtocost#IT networking#Electronics item#electronics and IT Supplier in uae#it retailer#it supplier#Fortigate 100f#Fortigate 80f#Fortigate 60f#best seller#sale#deals#offers#security#free delivery#dubai shopping#online shopping
0 notes
Text
#cyber security#united arab emirates#network solutions#techbee dubai#it solutions company in dubai#cyber threats#firewall security
1 note
·
View note
Text
Maximizing Network Performance: A Comprehensive Guide to GCP's Network Intelligence Center
Discover, monitor, and optimize your network with GCP's Network Intelligence Center! 🔍✨ #GoogleCloud #NetworkMonitoring #CloudOptimization
In today’s fast-paced digital world, a reliable and finely-tuned network infrastructure is absolutely vital for the triumph of any organization. As cloud environments grow more intricate, the task of overseeing and enhancing network performance can seem overwhelming. Yet fear not, for the Google Cloud Platform (GCP) presents an extraordinary solution: the Network Intelligence Center. Join us on…

View On WordPress
#azure#cloud#Cloud network management#Connectivity tests#Cybersecurity#Firewall insights#GCP Network Intelligence Center#google cloud platform#Internet intelligence#network monitoring#Network optimization#Network topology#Network troubleshooting#Networking#Packet mirroring#Performance dashboard#Reachability tests#Routing visibility#Security#VPN insights
1 note
·
View note
Text
Understanding the Firewall: Your First Line of Defense in Cybersecurity
Introduction -
It is critical to protect your network from cyber dangers in the connected digital world of today. Strong cybersecurity measures are becoming essential due to the constant risk of malware infections, data breaches, and unwanted access attempts. The firewall, a vital element that creates a barrier between your reliable network and the unpredictably vast internet, is at the vanguard of this protection.
Let me tell you What exactly a Firewall is :
Consider your network as a stronghold, with the firewall acting as the gatekeeper regulating access and departure. A firewall is essentially a software or hardware security system that keeps an eye on and regulates all incoming and outgoing network traffic by pre-established security standards. These rules serve as the first line of protection against potential threats by dictating which data packets are allowed to flow through and which are blocked.
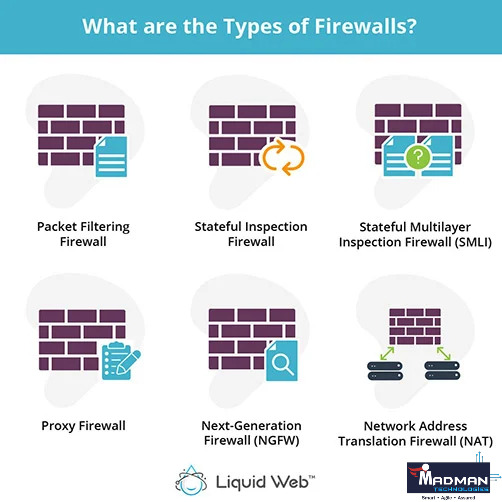
Types of Firewalls -
Firewalls come in various forms, each with its own set of functionalities tailored to meet specific security needs:
Packet-Filtering Firewalls: These inspect individual packets of data as they traverse the network, making decisions based on predetermined criteria such as IP addresses, ports, and protocols.
Stateful Inspection Firewalls: Building upon packet filtering, stateful inspection firewalls maintain a record of active connections and use this contextual information to make more informed decisions about allowing or blocking traffic.
Proxy Firewalls: Proxy firewalls operate as middlemen between internal and external network traffic, thoroughly inspecting data packets and enhancing security by masking internal IP addresses and adding more recording and analytic features.
Next-Generation Firewalls (NGFW): NGFWs offer complete security by fusing classic firewall functions with cutting-edge technologies. These characteristics include intrusion detection, application awareness, and enhanced threat protection.
The Role of Firewall in Cybersecurity -
A firewall's main function is to safeguard your network against the harmful activity, illegal access, and online threats. Firewalls assist in preventing intrusions, blocking malware infections, and reducing the dangers connected with a range of cyberattacks by enforcing security policies and filtering traffic by preset rules. These assaults include:
Denial-of-Service (DoS) Attacks: Firewalls can detect and block suspicious traffic patterns associated with DoS attacks, preventing them from overwhelming your network resources.
Malware infections: Firewalls can prevent efforts by viruses, worms, or other malware to infiltrate your network by screening incoming traffic for known malware signatures and dangerous behaviours.
Unauthorized Access Attempts: Firewalls can prevent efforts by viruses, worms, or other malware to infiltrate your network by screening incoming traffic for known malware signatures and dangerous behaviours.
Data Leakage: Firewalls help protect against data breaches and information leaks by granting granular control over outgoing traffic. This prevents sensitive data from leaving your network without the required authorization.
Best Practices for Firewall Implementation -
Firewalls are an essential part of cybersecurity, but how well they work depends on how well they are configured, maintained, and adhered to :
Define Clear Security Policies: Establish comprehensive security policies that outline the acceptable use of your network and the rules governing traffic flow.
Regularly Update Rulesets: Stay vigilant by updating firewall rulesets to address emerging threats and vulnerabilities, ensuring that your network remains protected against the latest cyber risks.
Monitor and Analyze Traffic: Implement logging and monitoring mechanisms to track network activity, detect anomalies, and identify potential security incidents in real time.
Combine with Additional Security Measures: Enhance your network security posture by complementing firewalls with intrusion detection systems (IDS), antivirus software, and other security measures.
Regular Audits and Assessments: Conduct periodic audits and security assessments to evaluate the effectiveness of your firewall configuration and identify areas for improvement.
Conclusion -
The firewall is the mainstay of network security in a time of ubiquitous cyber threats and digital connection. Firewalls are essential for protecting sensitive data, important assets, and the cybersecurity posture of your company because they efficiently manage traffic flow and enforce security standards. Accept the strength of firewalls as your first line of defence against the always-changing cyber threat landscape and provide your network the defence it needs.
One of the best sellers and service providers of firewalls is MADMAN TECHNOLOGIES, where A product must meet the following criteria to be eligible for the Firewall category:
Evaluate and filter user access;
Build barriers between networks and the internet; and
Notify administrators when unauthorized access is attempted.
Establish and uphold security and identification regulations.
Automate testing and monitoring-related duties
For any queries, you can google our website -
Contact details — 9625468776
#information technology#it products#it services#technology#itservices#it technology#application of firewall#it solutions#firewall#networking#secuity#network security
0 notes
Text
How to Protect Your Business From Cyber Threats
Cybersecurity is a major topic every business owner should be discussing. Here is some info from FRC that we hope helps.
Imagine we’re sitting down over a cup of coffee, and you’ve just asked me how to shield your trucking business from the ever-looming shadow of cyber threats. It’s a digital age dilemma, but I’m here to walk you through some straightforward strategies to bolster your defenses.
First off, let’s talk about the elephant in the room: cyber threats. They’re not just a problem for the tech industry;…

View On WordPress
#access control#antivirus software#cloud storage#cyber attacks#cyber threats#cybersecurity#cybersecurity laws#data protection#digital transformation#employee training#encryption#firewalls#incident response#legal compliance#malware#network security#password policies#phishing attacks#ransomware#secure communication#software updates#trucking industry#vendor security#VPN
0 notes
Text

#eeka#eekaconsultancyservices#consultancyservices#consultancy#services#bangalore#networking#firewall#security#happy#jobs#ecs#mothers day#motherslove#motherhood#mother
1 note
·
View note
Text
How to Allow IP Addresses through Firewall Linux?
Configuring IP Access with iptables
Verifying iptables Installation
Listing Current Firewall Rules
Allowing Specific IP Addresses
Saving iptables Rules
Creating a Secure IP Whitelist
Defining Your IP Whitelist
Configuring iptables Rules
Testing Connectivity
Streamlining Firewall Management with BeStarHost
Introducing BeStarHost
Using BeStarHost for IP Whitelisting
Best Practices for Linux Firewall Management
Regularly Review and Update Whitelist
Implement Fail2Ban for Additional Security
Conclusion:
Effectively managing your Linux firewall is an integral part of maintaining a secure server environment. By mastering iptables and understanding how to allow specific IP addresses, you fortify your defenses against potential threats. Whether you opt for manual configuration or utilize tools like BeStarHost, the key is to stay vigilant, update your rules regularly, and adapt your security measures to evolving threats. Implementing these practices will empower you to keep your Linux server secure and resilient.
To Learn More, Click this Link:
#Linux Firewall Configuration#IP Address Whitelisting#Linux Firewall Rules#Network Security on Linux#Firewall Tutorial
0 notes
Link
You must have heard about firewalls but do you know what they are used for? Firewall programs are designed to protect the #vulnerabilities of your internal network from unauthorized access to the #Internet.
0 notes
Text
youtube
SOPHOS XGS SW-19.5.3 MR-3 Firewall | First Time Configuration | Step by Step in Hindi | By Sachin
#firewall#sophos xg firewall#network security tutorial#sophos xg firewall complete overview in hindi#how to setup sophos firewall in hindi#how to create rule in the sophos xg firewall#how to install sophos firewall#how to install sophos firewall on vmware#sophos xg v19#sophos xg firewall v19#xg firewall#setup sophos xg v19#configure sophos xg v19#configuring sophos xg v19#v19#xg firewall v19#sophos firewall#what is firewall#firewall explained#network firewall#Youtube
0 notes
Text
1)Who is Ionix?
We are a full-service MSP (Managed Service Provider) based in Elk City, OK.
2)What does an MSP do?
If your school or business uses technology, we can help streamline your operations and protect you from security threats and equipment failure. We can do all of this for a fixed rate, so you don't have to worry about your system stability or your budget.
3)What can Ionix provide?
This is a hard question to answer because every business is different, and we customize our solutions to fit your needs.
Small list of what we can provide:
Network Solutions: Firewall, Switches, Cabling and Wireless Access Points
Hardware for each user: Computer, Monitor, battery backup
Security Awareness Training
PCI Compliance/Consulting
Security Cameras
Data backup solutions
#WIRING#technology#Switch#smartboard#security cameras#network#MONITOR#Managed Services#laptop#firewall#desktop#cloud#cabling#backup
1 note
·
View note
Text
Always On VPN November 2023 Security Updates
Microsoft has released its security updates for November 2023. For Always On VPN administrators, it’s a light month, with just a single CVE affecting Always On VPN infrastructure.
PEAP
CVE-2023-36028 addresses a remote code execution (RCE) vulnerability in the Microsoft Protected Extensible Authentication Protocol (PEAP). An attacker could exploit this vulnerability by sending a specially…

View On WordPress
#Always On VPN#AOVPN#authentication#CVE#EAP#firewall#Microsoft#mitigation#network policy server#NPS#PEAP#protected extensible authentication protocol#security#security update#update#VPN#vulnerability#Windows#windows firewall#Windows Server#workaround
0 notes
Text
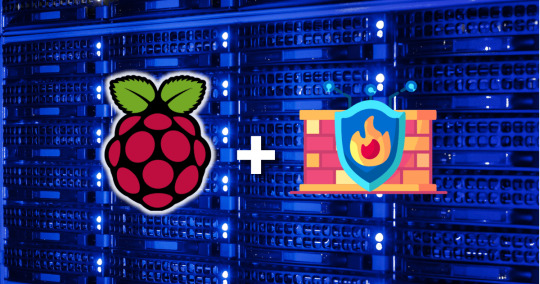
Raspberry Pi Firewall Command Line Configuration Step-by-Step
Raspberry Pi Firewall Command Line Configuration Step-by-Step #homelab #selfhosted #rapsberrypi #RaspberryPifirewallguide #UFWsetuponRaspberryPi #SecureRaspberryPinetworking #RaspberryPiUFWconfigurations #TroubleshootingUFWissues #RaspberryPifirewall
Raspberry Pi OS is an extremely popular self-hosting platform many use for running services. Let’s set the tone for Raspberry Pi firewall configuration via the command line and see what we will learn.
Raspberry pi os
What: A step-by-step how-to guide for UFW (Uncomplicated Firewall) on your Raspberry Pi
Where: You can use this on native Raspberry Pi devices or other platforms like virtual…
View On WordPress
#Easy firewall setup on Raspberry Pi OS#Essential UFW commands#Protecting Raspberry Pi with UFW#Raspberry Pi firewall best practices#Raspberry Pi firewall guide#Raspberry Pi network security tips#Raspberry Pi UFW configurations#Secure Raspberry Pi networking#Troubleshooting UFW issues#UFW setup on Raspberry Pi
0 notes
Text
Top 20 Technical Support Interview Questions and Answers for Freshers in IT
When applying for a technical support role in the IT industry, preparation is key to success. To help freshers ace their technical support interviews, we’ve compiled a comprehensive list of 20 common interview questions along with sample answers. These questions cover a wide range of technical topics and soft skills necessary for excelling in a technical support role.
What does technical support…

View On WordPress
#Antivirus#BIOS Update#Blue Screen of Death#DHCP#DNS#Firewall#Internet Connectivity#Interview questions#IP Address#IT Troubleshooting#Malware Protection#NAT#Network Security#Patch Management#Router#Subnetting#Switch#System Restore#Technical Support#Technology Trends#VPN
0 notes