#growth hacker
Text
2 notes
·
View notes
Text
3 growth hacks que qualquer um pode implementar
3 growth hacks que qualquer um pode implementar
Neto Angel é um verdadeiro Growth Hacker. Ele é um especialista em encontrar frutas escondidas que criam grandes saltos no crescimento.
A carreira de crescimento de Neto Angel começou no mundo do Luxo, trabalhando com várias startups desde o início até a venda. A maioria delas se concentrou em vendas tradicionais para crescimento. Neto Angel mudou-se para uma agência digital e começou a se…
View On WordPress
0 notes
Text
لمَ عليك ألا تُلاحق الأشياء البرّاقة الجديدة أثناء تعلّمك مجالًا أو مهارة؟ [3 أسباب وجيهة]
لمَ عليك ألا تُلاحق الأشياء البرّاقة الجديدة أثناء تعلّمك مجالًا أو مهارة؟ [3 أسباب وجيهة]
مساء الإسعاد وبُعْد الحسّاد،
اقترح عليّ الأستاذ خالد الصادق هذا الموضوع فشَكَر الله له:
https://twitter.com/khaledAlSadek1/status/1542143952874242048?s=20&t=rWsGTH_4oL7WZHDr4e2Kvw
بما أننا ذكرنا في العنوان الأشياء البرّاقة اللامعة الجديدة فهناك متلازمة لا بد أن تعرفها 👇
أولًا ما هي متلازمة ملاحقة الأشياء البرّاقة الجديدة؟
دعنا نقتبس تعريفها أو مفهومها من الزميل خالد الحرّاق مؤسس موقع شانية…

View On WordPress
#Animalz#content marketers#Copycat#Eric Gilliam#Erik Hoel#Gerard Holton#growth hacker#GROWTH97#information gain#Sean Ellis#Shiny Object Syndrome#The Growth Newsletter#موقع شانية#متلازمة الأشياء اللامعة#مجال#مخترق نمو#الاكتساب#التحصيل#اختراق النمو#تعلم#تعلم مجال#جيرار هلتن#جيرار هولتون#جيرارد هلتن#خالد الحراق
0 notes
Text
Pilot:

Finale:
#leverage#eliot spencer#alec hardison#parker#christian kane#aldis hodge#beth riesgraf#that's GROWTH baby!#pilot: yeah you're on your own bye#finale: i will die a thousand deaths before i allow them to come anywhere near you#lone wolf to pack-bonded#ot3: hitter hacker thief#ghostly'sgifs
585 notes
·
View notes
Text
keeley and jamie fighting about accountability in season 1 vs jamie taking accountability and apologizing to keely in season 3 🥹
#hes grown so much! and so has their relationship!! i love it!!#gonna make a gifset of this tomorrow#ted lasso#ted lasso spoilers#(also it wasnt jamies fault even though his password was password#its only the hackers fault#i just love that jamie wanted to apologize anyway#growth)
97 notes
·
View notes
Text
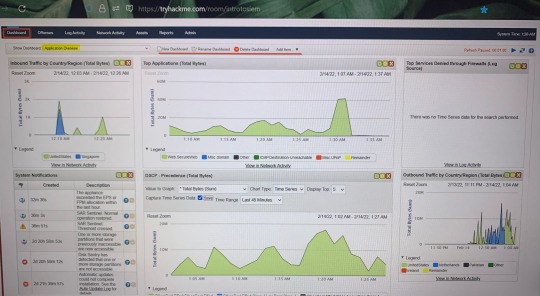
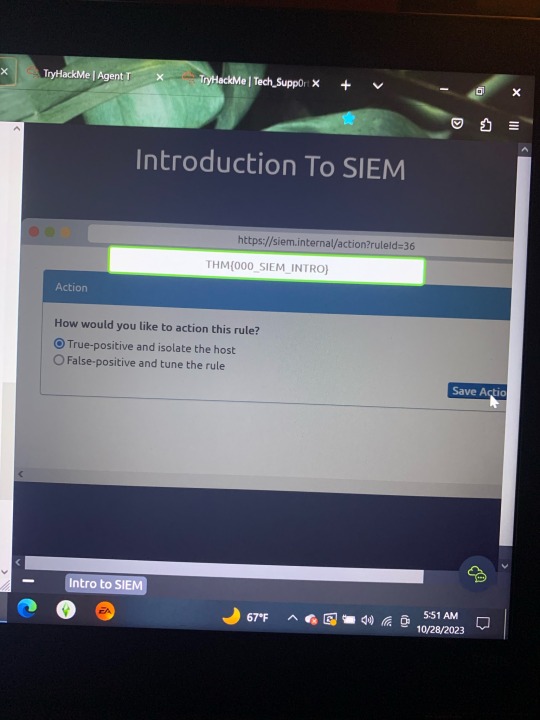

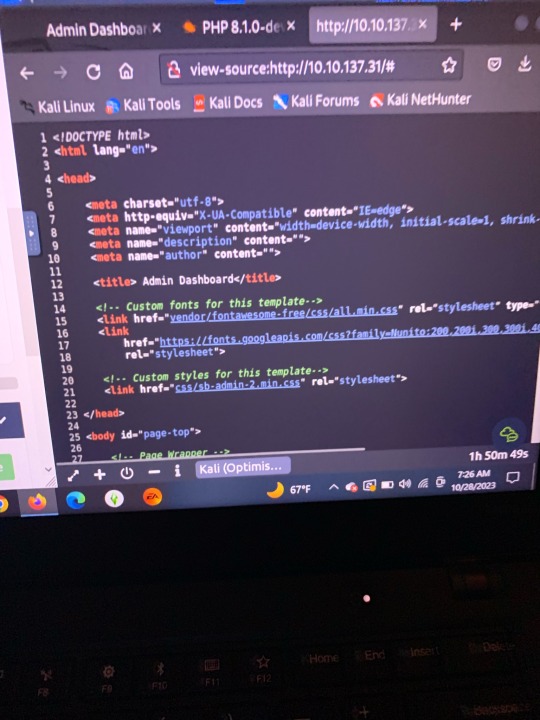
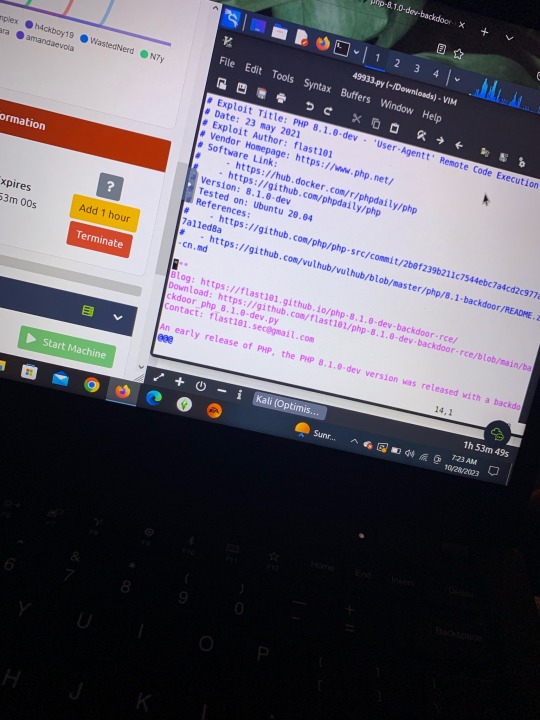
TryHackMe.. learning more of Nmap, Kali Linux, Burp Suite, etc. I am more a fan of defensive security/blue team (unpopular opinion) the first 2 pictures were walkthroughs of an SIEM (Security Information and Event Management).
#tryhackme#hacking#cool#blue team#red team#hacker#learning and growth#linux#kali linux#labs#tech#technology
3 notes
·
View notes
Text
Very excited for once upon a crime. To prepare for it I think I'm gonna watch leverage over again
#unprepared casters#once upon a crime#'vic whats lever-' IM SO GLAD YOU ASKED#its a show about a group of criminals (hitter hacker theif grifter mastermind) who hit the jackpot and never have to steal again#but they quickly get bored and decide to work together and get revenge on corrupt billionaires for people wronged by them (for free)#its kinda like cop shows in the constant predictable format but a thousand times better cause leverage is not copaganda#its great. there are some moments that you go uhhhhh at cause it is from 2008#but other than those few and far between bits its great#its great#theres a poly couple as canon as 2008 could allow. theres so much growth in all of the characters. everyone is like so pretty#in the human way not the everything-photoshoped-perfect way#they steal a mountain twice. different mountains.#they do a bank heist WHILE its being stood up AND frame the bad guy they had alreadly did a con on for it and also for doing meth as bonus#they land a hacked plane while 4/5 of the team is on the plane and the 5th fixes it while pretending to be an office worker so convincingly#that the office throws him a birthday party#they do a The Office themed epsiode and the subplot of the hacker eating the hitter sandwich is a metaphor for their relationship#the asshole on the team gets forcibly adopted AND shot several times. about once a season.#its a great fun time. the reboot is great too its very gay in the 2021 way#also if you need anything else to convince you that its good#i stayed up for like 3 days straight only watching it start to finish all 5 seasons and started hearing the background music while paused#and do not regret it#pretty sure i started a rewatch later that same week
14 notes
·
View notes
Text

#adventure#outdoors#politics#scott morrison#science#stray kids#sky#hacker noon#facebook warns of huge cyberattack spike linked to russia as hackers target accounts of ukrainian military personnel#growth hacking#shrek 2#plants#snow#hacking
4 notes
·
View notes
Text

#entrepreneurship magazine#entrepreneurship#business innovation#entrepreneurial mindset#success in small business#leadership success#low cost business ideas with high profit#business investment opportunities#entrepreneurial journey#startup ecosystem#growth hacking#entrepreneurship culture#growthhackers#tech entrepreneurship#entrepreneurial ventures#growth hackers digital#entrepreneurial leadership
0 notes
Text
cybersecurity has become an increasingly important issue for individuals
organizations in recent years. With the growing reliance on technology and the internet, the risks of cyber attacks, data breaches, and online fraud have also increased significantly.
Individuals are at risk of cyber attacks such as identity theft, phishing scams, and malware infections, which can compromise personal information, financial data, and other sensitive data. Organizations face similar threats, but on a larger scale, as they have to protect their customers' data, intellectual property, and business operations from cyber threats.
Cybersecurity measures, such as firewalls, antivirus software, and encryption, are essential to prevent cyber attacks and protect sensitive data. Individuals and organizations also need to be aware of cybersecurity best practices, such as creating strong passwords, being cautious when sharing personal information online, and regularly updating software and security systems.
In addition, cybersecurity professionals play a critical role in identifying and mitigating cyber threats. As the demand for cybersecurity experts continues to grow, there are many opportunities for individuals to pursue careers in this field and help protect individuals and organizations from cyber attacks.
0 notes
Text
A crescente importância da inovação de valor para a criação de um novo Growth
A crescente importância da inovação de valor para a criação de um novo Growth
Com recursos limitados à mão, as empresas precisam permanecer inteligentes e eficientes quando se trata de investir em inovação.
Este é um momento desafiador para muitas empresas. Por um lado, a interrupção da cadeia de suprimentos, a escassez de mão de obra, os aumentos dos preços das matérias-primas e da energia estão elevando os custos das empresas. Por outro lado, a demanda está fraca devido…

View On WordPress
0 notes
Text

How To Choose The Right Business Solutions For Investors And Entrepreneurs
To choose the right business solutions for investors and entrepreneurs, one needs to understand the elements: Identity and Analyzing the problem, search benefits, and finding opportunities.
#business solutions for investors and entrepreneurs#startup investments in India#Find a Growth Hacker for Your Startup#seed funding companies in gurgaon
0 notes
Text
Hey at least this time I played 5v5 in league I laughed at the trolling and took pleasure in robbing the enemy team the pleasure of breaking our Nexus Crystal themselves.
Usually I tilt beyond rationality.
Progress.
#celebrate the little milestones#being able to find zen in the toxic wasteland that is the League community is a hell of a feat id say#healing#growth#be proud of any step towards mental stability#unexpected positive kaosposum#leblanc is still the houdini burst queen#you have just enough time to register her at the edge of your screen#and by the time youve realized Leblanc has Entered The Chat#youre already watching your death timer#i laughed the entire match because of that#shes still broken af#Some Things Never Change#btw keep in mind i usually play bot matches#real 5v5 usually sends me into a full panic attack#Having the chat off helps that a lot#having clarity bc you laugh off all the stupid shit makes it 1000000000x easier to spot actual hackers btw
0 notes
Text
youtube
{Filed Under: Literally everything I've been trying to explain since 2k15's Tri dropping + Kizuna, GhostGame, "The Beginning" being pre-viewed,
+ DGMN Survive..., ReArise, any upcoming GAME[S]...}
(BUT ALSO SINCE Tamers, Frontier, Savers,
Xros Wars, Young Hunters!.....)
[Even if it's more game-related,
the other (animated) series fit with this mindset Too]
(It's short but worth a watch!)
{This post is marked with 'no rb',
but 'Likes' are O.K.!
+ Feel free to share the link around on your own!}
#izzyizumi refs#izzyizumi no rb#dgmn relevant#rearise relevant#survive relevant#dgmn games relevant#(Filed Under: Things The Entire DGMN Standom NEEDS to SEE)#(THANK For Putting It Into Words)#growth is not bad#(I haven't had enough focus to play Cyber-Sleuth or Hacker's Memory yet myself but I'm also)#(Particularly Thinking About)#(Survive)#(by sharing this)#(BUT ALSO)#(rEArISE Got A Lot Of ~Criticisms~ even on the chara designs Too Back Then Which Still Astounds Me)#(And Yes Adventure is the oldest of main series but 02-taking-place-in-2002 also Technically COUNTS there as 'older')#(Meanwhile Adventure already got its own re boot SOOOO.....)#dgmn wonderswan relevant#(I'll agree the W.S. ones too also count on 'older' end but I've seen ppl absolutely rEFUSING the idea of even porting it)#(even though they said they were OPEN to possibility of AT LEAST ports if not re masters or re makes)#(I or other W.S. interested fans didn't make that up! They've alrEADY SAID IT???)#(and I'm just '??!????!')#(at negative comments and Takes I constantly see abt that TOO)#(OK ANYWAY Everyone Needs To Watch This)#(It was cool at least even a tiny moment of K.H.3 got shown here!)
0 notes
Text


#bheem rathore#bheem rathore growth hacker#bheemrathore.com#bheem rathore defence startup#bheemrathore
0 notes
Quote
growth hacking, ebook, growth hacker, internet marketing, SEO, marketing, internet, growth hacking, wealth, technology
How To Promote Your Business Growth Hacking: Overall Health:
0 notes