#cryptogram
Text

20-18-21-19-20 13-5! F hklt dszg rn 20-1-12-11-9-14-7-0-1-2-15-21-20!
#doodle#gravity falls#gravity falls fandom#bill cipher#gravity falls bill#stanford pines#ford pines#ford gravity falls#Stanford gravity falls#bill cipher gravity falls#decode#cryptograms#cryptogram
70 notes
·
View notes
Text
5,6:2 – 9:1,5
5,8:3 – 9:4 – 8:3 – 9:5 – 6:2
8:1,4
9:4 – 16,5,2,26:2
8:4 – 11:3
14,26:2
3:2 – 8:4 – 9:5,4,2 – 5,2,26:2
6 notes
·
View notes
Text









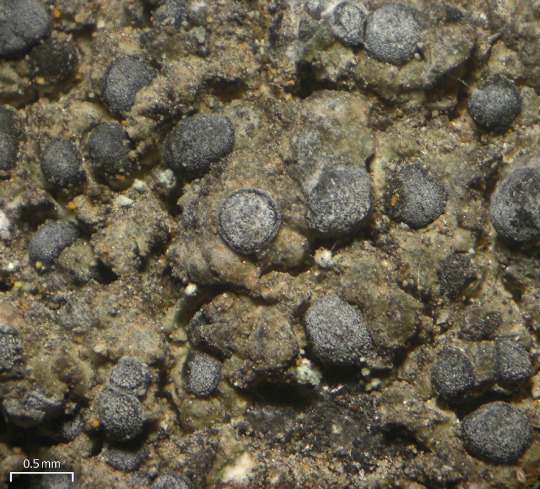
Diplotomma alboatrum
Raise your hand if you love morphologically variable whitish crustose lichens with black apothecia!!! . . . No one? Really? OK well, I guess I can see why. There are like, a bajillion of them, with few distinctive traits between them. So when D. alboartum decides to just throw convention to the wind and vary in thallus texture, pattern, color, apothecial morphology, and preferred substrate, it's just like "c'mon dudes, give me a break." Just to make you work a little harder, this confusing little assemblage of organisms can be identified by examining its spores under a microscope:

They are distinctively brown, submuriform to muriform (patterned like a brick wall), and ellipsoid. Thanks bud. Real helpful. I still love you.
images: source | source | source | source
info: source | source
#lichen#lichens#lichenology#lichenologist#lichenized fungus#fungus#fungi#sysmbiosis#algae#mycology#cryptogram#biology#ecology#botany#bryology#life science#environmental science#natural science#nature#naturalist#beautiful nature#weird nature#science#scientist#science side of tumblr#trypo#trypophobia#Diplotomma alboatrum#Diplotomma#I'm lichen it
31 notes
·
View notes
Text
We Figured Out the Cryptograms in the Haunted Mansion Queue!
Bonus article! Remember yesterday's post about the Haunted Mansion cryptograms? We'll tell you what they say and how we figured it out!
Yesterday on our Disney Rover Facebook page (did you know we have a Facebook page?) we shared two cryptograms found in the Haunted Mansion queue. These two pictures came from another group page (and we’d give them credit if we remembered which group). We’re assuming these are in the extended queue, so if crowds are light or there’s a low wait time, chances are you may not pass these.
During a…

View On WordPress
#cryptogram#Disney#Disney Haunted Mansion#disney queue#disney queue line#Disney World#Haunted Mansion#haunted mansion disney#haunted mansion puzzle#Magic Kingdom#Walt Disney World
4 notes
·
View notes
Text
The Guardian has published a collection of anecdotes about Alan Rickman. Here is part of what Eddie Izzard had to say (visit the link above to read more):
I first met Alan after a benefit show at the London Palladium in 1994. At that time, I knew and loved his work in Die Hard: the seriousness but lightness of touch. I remember chatting to him after and telling him that I really wanted to do dramatic acting, my first love. He said he didn’t think I was crazy, which was nice of him, but we left it at that. Next, I was suddenly told Alan had suggested my name to play opposite Lindsay Duncan in a David Mamet play. It was a wonderful thing for him to do and Lindsay was a fabulous actor to be working with.
The play to which she is referring is “Cryptogram”. (Photo source: imsvintagephotos.com)
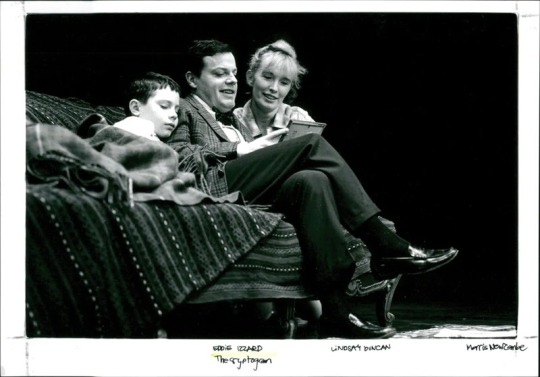
Lindsay Duncan and Eddie Izzard will be appearing together again in the upcoming film “Doctor Jekyll”.
#eddie izzard#alan rickman#lindsay duncan#cryptogram#the guardian#doctor jekyll#link#article#acting#photo#1994#stage
43 notes
·
View notes
Link
Rivers Cofield, an archeological curator who lives in Chesapeake Beach, Maryland, had bought the dress while visiting her mother in Searsport, Maine. She didn’t think much about it after her blog post.
But unbeknownst to her, curious amateur sleuths were working to solve the mystery. They dubbed it the “silk dress cryptogram” and floated conspiracy theories about the words. Some speculated that Bennett was a spy using coded words to communicate.
In 2017, one blogger added the note to his list of the Top 50 unsolved encrypted messages and floated more theories. Was it a cryptic love note? Dress measurements? Civil War codes?
Rivers Cofield quickly dismissed any interpretation linked to the Civil War. She has studied 1880s catalogues from department store chain Bloomingdale’s, and had no doubt the dress was from that era. By then, the war had been over for about 20 years.
But then a Canadian researcher cracked the code
2 notes
·
View notes
Text
"Bismark Omit leafage buck bank."
2 notes
·
View notes
Text
ok a weird little thing . i’ve made a poem which is a spoiler for WotM , but a deceiving one . but i decided that was too easy . so if you want the spoilers …

come get ‘em i guess
#rottmnt#rise of the tmnt#rise of tmnt#rise tmnt#rottmnt fandom#rottmnt leonardo#rottmnt leo#tmnt fandom#rottmnt raph#rottmnt raphael#text#text tag#textpost#text post#puzzle#cryptogram#rise fanfic#rottmnt fanfiction#rottmnt fanfic#unpause rise of the tmnt#save rise of the teenage mutant ninja turtles#save rise of the tmnt#rise of the teenage mutant ninja turtles#rise of the tmnt leo#rise of the turtles#leonardo rottmnt#rottmnt angst#save rottmnt#support rottmnt#wotm tag
8 notes
·
View notes
Text
Divisions of Codes and Ciphers
There are two kinds of codes/ciphers: transpositional, where your characters are the same, just moved about (like an anagram with a precise way to revert the encrypted text to the message), and translational, where your characters are in the correct position, but it's not the same characters (like a masquerade party).
The earliest transpositional cipher one would normally think of is good old Scytale. Imagine you have a tube, and wrapped around said tube is a strip of cloth. You have to make two decision:
- How many sides does the Scytale have?
- How many times can you wrap the strip of cloth around the tube?
You have that? Good. Now, you write your message on the strips on the tube. For me, my Scytale has six sides, and I can wrap my strip four times around.
After you've done this, you can unwrap the strip of cloth. What you should see is a bunch of characters with no rhyme or reason to it. The receiver, on receiving the strip of cloth, would wrap it around a tube of similar dimensions, and they would be able to read the message.
My encrypted text: WSEARLIHSYULLIAFSLNWOA
The earliest translational cipher one would normally think of is our friend Caesar. Shift forwards/backwards by a number less than 26 (the number of letters in the English alphabet) to get a completely new one.
My encrypted text: JURA GURER'F N JVYY, GURER'F N JNL.
While these are good in their time, there's just one problem if you use it now: It can be bruteforced.
What do I mean by bruteforce? Well, let's look at the case for Caesar.
Since Caesar only has 26 possible configurations (assuming you're using the normal, unchanged alphabet), you can simply write out all 26 configurations, and see which one looks the most intelligible.
For "JURA GURER'F N JVYY, GURER'F N JNL", it'll end up something like this.
KVSB HVSFS'G O KWZZ, HVSFS'G O KOM.
LWTC IWTGT'H P LXAA, IWTGT'H P LPN.
MXUD JXUHU'I Q MYBB, JXUHU'I Q MQO.
NYVE KYVIV'J R NZCC, KYVIV'J R NRP.
OZWF LZWJW'K S OADD, LZWJW'K S OSQ.
PAXG MAXKX'L T PBEE, MAXKX'L T PTR.
QBYH NBYLY'M U QCFF, NBYLY'M U QUS.
RCZI OCZMZ'N V RDGG, OCZMZ'N V RVT.
SDAJ PDANA'O W SEHH, PDANA'O W SWU.
TEBK QEBOB'P X TFII, QEBOB'P X TXV.
UFCL RFCPC'Q Y UGJJ, RFCPC'Q Y UYW.
VGDM SGDQD'R Z VHKK, SGDQD'R Z VZX.
WHEN THERE'S A WILL, THERE'S A WAY
XIFO UIFSF'T B XJMM, UIFSF'T B XBZ.
YJGP VJGTG'U C YKNN, VJGTG'U C YCA.
ZKHQ WKHUH'V D ZLOO, WKHUH'V D ZDB.
ALIR XLIVI'W E AMPP, XLIVI'W E AEC.
BMJS YMJWJ'X F BNQQ, YMJWJ'X F BFD.
CNKT ZNKXK'Y G CORR, ZNKXK'Y G CGE.
DOLU AOLYL'Z H DPSS, AOLYL'Z H DHF.
EPMV BPMZM'A I EQTT, BPMZM'A I EIG.
FQNW CQNAN'B J FRUU, CQNAN'B J FJH.
GROX DROBO'C K GSVV, DROBO'C K GKI.
HSPY ESPCP'D L HTWW, ESPCP'D L HLJ.
ITQZ FTQDQ'E M IUXX, FTQDQ'E M IMK.
JURA GURER'F N JVYY, GURER'F N JNL.
As you can see, the 13th one in the list is the one that is the most legible. If you don't know a key, you can bruteforce it. If there's not a lot of possibilities, then you get this situation, which both Scytale and Caesar has. Scytale fares a bit better, but it is still bruteforceable.
But there is a way to make the Caesar a bit stronger: key it.
There are 26 letters of the alphabet, so there are 26! (26 factorial, basically the product of every number from 1 to 26) alphabets to choose from. The normal progression of the alphabet is but one of the ways to choose.
The problem with that, however, is that it's still very, very crackable. Anyone who has played Cryptogram before knows how easy it is to crack it without a key. Even if you have to use bruteforce to check, it's still rather solvable.
So we have to ramp it up somehow, but how?
Enter: bigrams, trigrams, and polyalphabetic ciphers
7 notes
·
View notes
Text
Bubbles on the bottom of a water glass resemble unknown script
#weirdcore#liminalcore#surrealcore#unreality#dereality#cryptogram#magic runes#strange phenomena#cryptidcore#naturecore#message in a bottle
4 notes
·
View notes
Text
Introducing a burst of joy with my vibrant and playful NFT design 'Cosmic Kaleidoscope: Enigmatic Blooms':
#artworld #contemporaryart #cryptogram #cyberpunk #minimalart #myart #onlineart #openseanftart #acidmit #nftart
#artworld#contemporaryart#cryptogram#cyberpunk#minimalart#myart#onlineart#openseanftart#acidmit#nftart
1 note
·
View note
Text







Made with cryptogram and photoroom - free to use!


More ship candy hearts
#candyheart#lesbianlovelife fanwork#lesbianlovelife post#lesbianlovelife#berena#holby city#berena valentine#wlw valentine#cryptogram
3 notes
·
View notes
Text
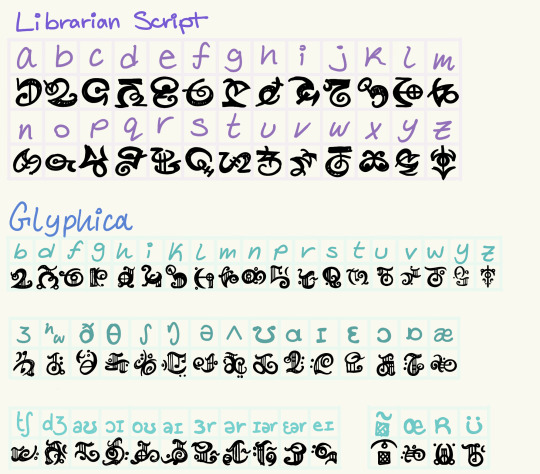
For those who like puzzles, here is a key for the cryptogram I plan to use in some of my works! I put a lot of work into this; it took me around four years to get to this point.
In essence, Glyphica is a language based in IPA with Librarian script acting as an in-between for that and the English alphabet. Also, please do not reuse this cipher as a fictional language. But you can have fun with it in any non-media way; just tag me so I can see it too!
This is something that will make up a significant part of my future Beastiary project c:
4 notes
·
View notes
Photo

Hey guys, check out our latest video- Binance Leading Web3 Fundings | Law enforcement inquiring surging for Coinbase | DIMO launches mainnet | 13% Americans holding crypto 🔰Credits to the original news content sources- 1- Binance Labs Leads Funding Round For Web3 Project- https://bitcoinist.com/binance-leads-funding-web3-project/ 2- Coinbase report shows dramatic increase in law enforcement enquiries worldwide- https://cointelegraph.com/news/coinbase-report-shows-dramatic-increase-in-law-enforcement-enquiries-worldwide 3- Decentralized automotive insight network DIMO launches mainnet- https://www.theblock.co/post/193837/decentralized-automotive-insight-network-dimo-launches-mainnet 4- 13% of Americans have now held crypto: JPMorgan research- https://cointelegraph.com/news/13-of-americans-have-now-held-crypto-jpmorgan-research ———————————————————————————————————————————————— 🔰If you Want to get 100 USDT, Register on the world's biggest crypto exchange- Binance and deposit more than $50 into your account. We'll both get a 100 USDT cashback voucher! 👉 https://bit.ly/bobinance #️⃣ Let's connect on Social Media:🌎 : 👍All links here (IG, Twitter, etc) - https://linktr.ee/cryptoikonmedia 📼 Also Streaming on Theta: https://www.theta.tv/cryptoikonmedia 💼 Business Inquiries: [email protected] 😎 Common username on all other major platform: @cryptoikonmedia 🔰About us: Crypto Ikon Media is a full-service Interactive #Crypto Media Agency. We provide 360-Degree Digital Branding & Marketing services to (Crypto, Defi, NFT, Web3, Metaverse & Blockchain) projects and companies. ———————————————————————————————————————————————— Disclaimer: Our content is not financial advice, legal advice or tax advice in any way, shape or form. Please do your own research. DM for credit or removal request (no copyright intended) ©️ All rights and credits reserved to the respective owner(s) . . . . . . #cryptocommunity #vechain #cryptoassets #criptotrading #tokenization #exchanges #blockchaingames #cryptokitties #ethereumproject #blockchaindevelopment #blockchainsolutions #earncrypto #airdropalert #cryptology #zilliqa #cryptogram #ftse #mainnet #instabitcoin #blockchain (at Delhi, India) https://www.instagram.com/p/CmHgeQbI3d5/?igshid=NGJjMDIxMWI=
#crypto#cryptocommunity#vechain#cryptoassets#criptotrading#tokenization#exchanges#blockchaingames#cryptokitties#ethereumproject#blockchaindevelopment#blockchainsolutions#earncrypto#airdropalert#cryptology#zilliqa#cryptogram#ftse#mainnet#instabitcoin#blockchain
1 note
·
View note
Text

DO YOU HAVE TO CHANGE THESE LINES TO AVOID COPYRIGHT ISSUES, BECAUSE THAT IS NOT THE QUOTE
0 notes